Security of Digital Assets Using BlockChain
Overview
As a body of technologies, processes and practices cybersecurity is designed to protect networks, computers, programs and data from attack, damage or unauthorized access. But, One of the most problematic elements of cybersecurity is the quickly and constantly evolving nature of security risks.
Adam Vincent, CTO-public sector at Layer 7 Technologies, describes the problem:
“The threat is advancing quicker than we can keep up with it. The threat changes faster than our idea of the risk. It’s no longer possible to write a large white paper about the risk to a particular system. You would be rewriting the white paper constantly…”
Analytics: Network Breach Activities
In 93 percent of cases, it takes attackers few minutes or even less to compromise systems. However, organizations can take weeks or more to discover a breach even occurred.
It is important for our government organization to have a real-time analytics platform in place that helps continuously detect potential breaches inside and outside the firewall.
According to Forbes, the global cybersecurity market reached $75 billion for 2015 and is expected to hit $170 billion in 2020. Now, when a huge amount is at stake for even more valuable data, Is it any good to say that the threat will always be there ? Not if, there is a technology like Blockchain available.
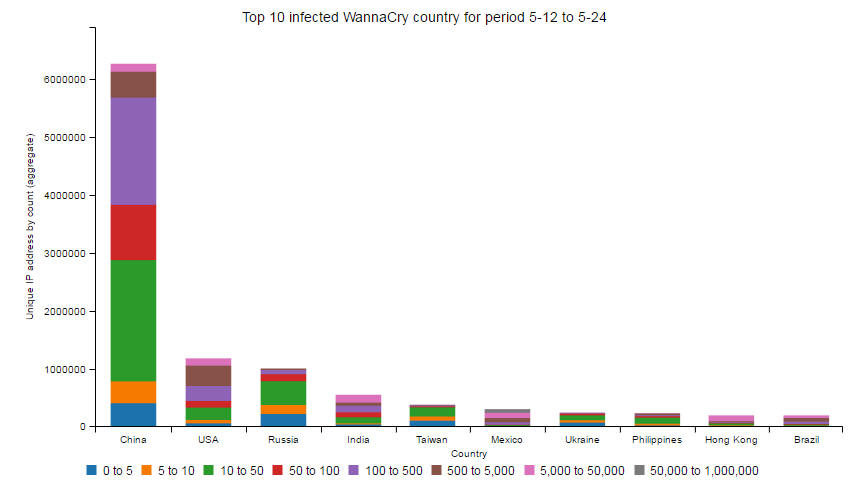
WannaCry: the biggest ransomware attack in history
WannaCry (also known as WanaCrypt0r and WCry), which was a new variant of the Ransom.CryptXXX family of ransomware, hit companies and individuals across the globe on May 12, 2017.
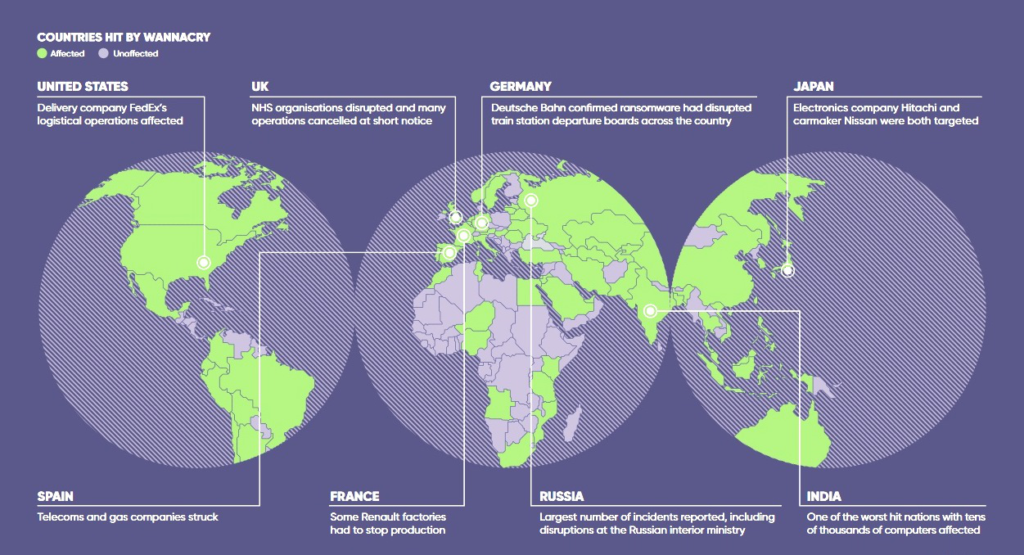
WannaCry’s major platform hit across the globe was Microsoft Windows XP operating system as it exploits a vulnerability in the platform, security updates for which were stopped in 2014.
It can encrypt 176 different file types and asks victims to pay in the form of Bitcoins which is most popular cryptocurrency. If payment is not made, the ransom would double after three days; if payment is not made in seven days, the encrypted files would be erased. While victims have been advised not to pay, funds are still being sent to the ransomware attackers.
Other big malicious attacks …
Another breach that held in 2016, was when Hackers stole the personal data of 57 million Uber customers and drivers over the course of a year, the company admitted in a blog post and confirmed that the data breach included names, email addresses, and phone numbers of about 50 million Uber riders and the personal information of 7 million drivers. Keypoint of this breach was that it included 600,000 license numbers however no social security numbers and no details about rides.
Blockchain: The technology behind Bitcoin
Fig: A new paradigm for computing
Blockchain which emerged as a disruptive technology has shifted the discussion around the applications for the technology, seven years after it was invented. However, this year the discussion has shifted more and more towards blockchain’s core elements and how its nature can be leveraged as distributed ledger.
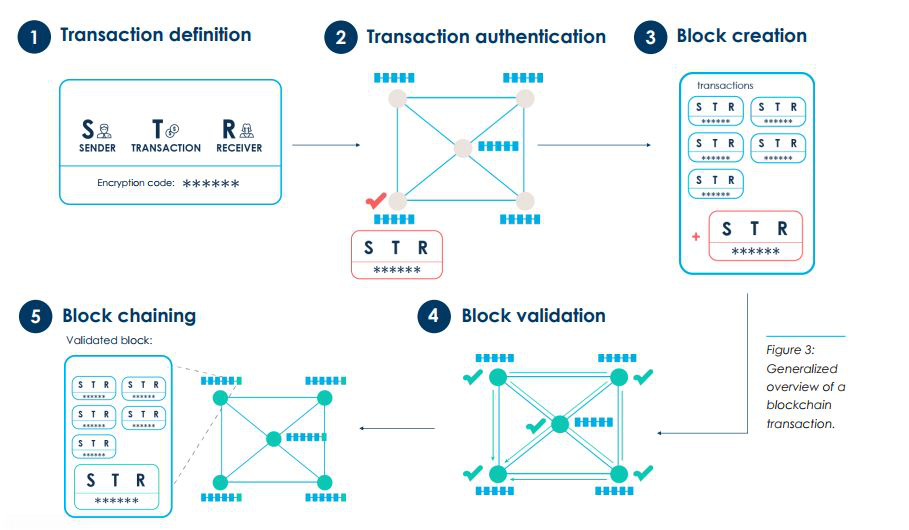
Bitcoin as an idea had the ability to transmit value at a distance without the permission of third party. This is the core of what blockchain technology makes possible. It is the technology underlying other cryptocurrencies and smart contract systems like Ethereum. Built around the concept of distributed consensus ledger, where the ledger is kept and maintained on a distributed network of computers, blockchain facilitates the movement of assets across the world in seconds, with only a minimal transaction fee. These assets can be any type of value as long as they can represented digitally.
Digital Assets: And, their part in digital economy.
Digital assets are a relatively recent development related to the spreading use of information technologies in the financial services. Digital asset is a floating claim of a certain service or goods ensured by the asset issuer, which is not linked to a particular account, and is governed using computer technologies and the Internet, including asset issuance, claim of ownership, and transfer. Digital assets have numerous use cases, including:
- Shares and financial securities
- Smart property
- Tie to a fiat currency
- Local community money
- Digital collectibles
- Access and subscription to certain resources.
For India, Digital payments, cyber security and Internet of Things — all of which are expanding at a significant pace — are expected to touch USD 50 billion, USD 35 billion and USD 20 billion, respectively. Inception of digitisation in Indian economy has set the government’s expectations to make India USD 1-trillion digital economy by 2022, which is surpassed by technology companies who stated that it has the potential to grow up to USD 4 trillion during the period. With that in mind, digital assets will surge in number, making the assets highly likely available to fingertips through smart devices and PDAs (personal digital assistant) and vulnerable to prominent cyber threats as well.
Blockchain for ensuring Digital Asset security
Using blockchain infrastructure for digital asset management enables creating pure digital assets (i.e., self-sufficient assets not acting as a “proxy” for real-world assets), which could be considered a transformative technology . Digital asset management could leverage security properties of blockchains, which include:
- Impossibility of counterfeit
- Immutability
- Disintermediation and ease of transfer
- Transparency and ease of auditing
- No overhead related to transaction processing
- Network effect brought by the unified infrastructure for multiple types of tokens
Since 2015, Lockheed Martin, a United States defense and security company and Guardtime Federal, a blockchain and cryptography company have conducted demonstrations of data integrity technologies to address the threat of manipulation in networked and weapon systems and embedded cyber physical systems. The two companies have been engaged in on-going assessments to address the continued evolution of cyber-focused threats across the entire development and fielding lifecycle.
With this effort, Lockheed Martin becomes the first U.S. defense contractor to incorporate blockchain technology into its developmental processes, enabling more efficient and assured offerings to the federal government.
Blockchain-based digital assets could be used in both financial contexts and in emerging consumer-to-consumer markets and Internet of Things (IoT).
The data a team creates, collects and disseminates across wide range of devices or platforms is usually checked for the minimum requirements for a ledger for digital assets, which are:-
- User security: The ledger needs to implement adequate authorization protocols to identify ownership and permit transfer or issuance of assets
- Counterfeit resistance: The system needs to have mechanisms to ensure impossibility of counterfeiting assets
- Auditability: The system needs to store all asset transactions in order to permit audits of activity (e.g., by regulatory bodies)
One category of digital assets are electronic money, where the asset is a claim to a real-world currency. Centralized electronic money systems (PayPal, WebMoney, Google Wallet, Apple Pay, etc.) are commonly used in e-commerce systems and they necessitate significant investments into back-end infrastructure, user authentication and regulatory compliance, therefore making them difficult to deploy and maintain for small and medium enterprises (SMEs).
Blockchain-based ledgers provide an alternative to centralized digital asset management. Blockchain technology allows to decouple the basic tasks performed by centralized e-money processors. These tasks include:
- Transaction processing: This could be performed in a decentralized manner by geographically distributed nodes of the network. Moreover, defining the rules for transaction processing (i.e., defining valid transactions) could be split from the processing
- Asset issuance: In the most general case, this could be performed by any user of the blockchain network.
- Securing user’s funds: This could be performed by third parties using custodial or noncustodial wallets.
- Identities of services (and optionally customers): This could be established by building public key infrastructure based on a blockchain
- Application development: This does not require cooperation with blockchain maintainers
How does network security is ensured ?
A public blockchain network provides three security modes for constituent nodes:
- Full verification nodes that verify and store every transaction circulating in the network. This security mode could be used by blockchain notaries, regulators, auditors, analytical services and dedicated “blockchain as a service” providers
- Simplified payment verification (SPV) nodes, which would be used by a vast majority of end users, as this security mode requires little computational resources and memory space
- Partial verification nodes made possible with the help of segregated witness and fraud proofs . These nodes could verify a small percentage of transactions (e.g., 1%), while contributing to the overall security of the blockchain network. Partial verification nodes could be operated by service providers on the blockchain
References:
https://blogs.adobe.com/adobeingovernment/cyber-defense-how-to-protect-your-most-valued-digital-assets-in-2016/ Steve Gottwals, Technical Director of Security Solutions, Adobe Systems Federal
http://news.lockheedmartin.com/2017-04-27-Lockheed-Martin-Contracts-Guardtime-Federal-for-Innovative-Cyber-Technology#assets_117 Lockheed Martin Contracts Guardtime Federal for Innovative Cyber Technology
https://www.uber.com/newsroom/2016-data-incident/ 2016 Data Security Incident
https://economictimes.indiatimes.com/news/economy/indicators/digital-economy-can-reach-4-trillion-in-4-years-tech-sector-to-government/articleshow/59188885.cms Digital economy can reach $4 trillion in 4 years: Tech sector to government
Leave a Reply